
Phishing, ransomware and zero-day exploits: attacks are not only occurring more frequently but they are also becoming more sophisticated all the time. Small and medium-sized enterprises in Germany in particular find that their IT resources are limited but their requirements are increasing – in the office, when working from home and when interacting with external partners. We will help you to develop and put together an information security structure: from establishing the current situation and drawing up a robust security concept to implementing technical and organisational measures. When doing this, we take on-prem, hybrid and cloud-based working into account – with a clear focus on cloud transformation and cloud-first/cloud-only solutions (e.g. Microsoft 365 and Azure).
To introduce our end-to-end unitop business solutions, we offer comprehensive IT security advice: we will develop a suitable roles and authorisation concept, define protective measures on a technical and organisational level and work with you to ensure that implementation goes to plan – so that your processes and data are protected right from the outset.
Innovating. Secure. Ready to succeed.
IT security consultancy – our services at a glance
How we work
Here’s how we create transparency and set priorities within your IT security
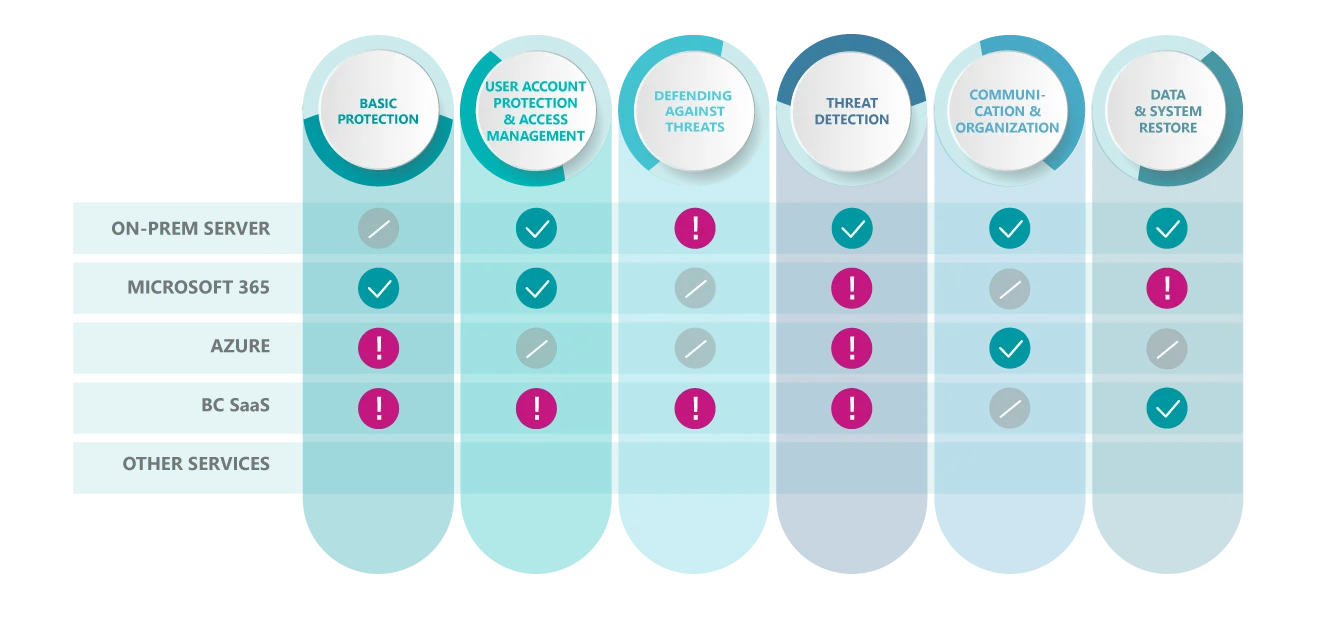
Our work begins by determining the current situation: we will take a look at the services and systems you are using (such as on-prem servers, Microsoft 365, Azure, SaaS applications or additional platforms) and assign relevant security measures to six key domains (from basic protection and identities/access to recovery).
The checklist that we use is expandable for good reason: new services can be added at any time so that your security assessment can continue to grow in line with your IT landscape. The result of this is a prioritised action plan – from quick wins to the long-term road map.
Note: We focus on carrying out an audit and architecture and configuration reviews, as well as action planning and implementation. Our portfolio of services does not include penetration tests.
Innovating. Transforming. Succeeding.
The way we work when providing IT security consultancy: from approach to implementation
Outcomes: IT security that works day in, day out – and can be relied upon whenever an incident occurs
Contact
Requesting IT security consultancy – Your contact
Are you looking to improve your IT security in a structured way – from a risk analysis to implementation and cloud security? We will be happy to advise you and work with you to clarify which approach makes most sense for you.






