
A security concept is more than just a collection of individual measures: it is your road map that sets out how IT security in your organisation will function from that point onwards – from a technical, organisational and operational perspective. In small and medium-sized enterprises in Germany in particular, a security concept needs to be one thing above all – suitable for everyday use. It must be capable of being implemented at a reasonable cost, responsibilities must be clearly laid down and it must not slow down ongoing operations.
Whether on-prem, hybrid or cloud: we work with you to develop a security concept that includes security architecture that reflects your actual environment and provides structured support for the transformation towards cloud-first/cloud-only. The result is a vision that translates security objectives into specific protective measures (controls) and serves as a foundation for implementation and operation.
Digitalising small & medium-sized enterprises.
Your security concept: tailor-made, not off the peg
Mature on-prem structures, hybrid transitions, new cloud services and SaaS applications are often being used in parallel: your initial situation will determine what measures actually make sense. That is why the security concepts we develop are not abstract, but take account of your processes, your critical systems and your cloud objectives. We can then create a security framework that will continue to be feasible on an everyday basis – and act as a guide when serious incidents occur.
Innovating. Transforming. Succeeding.
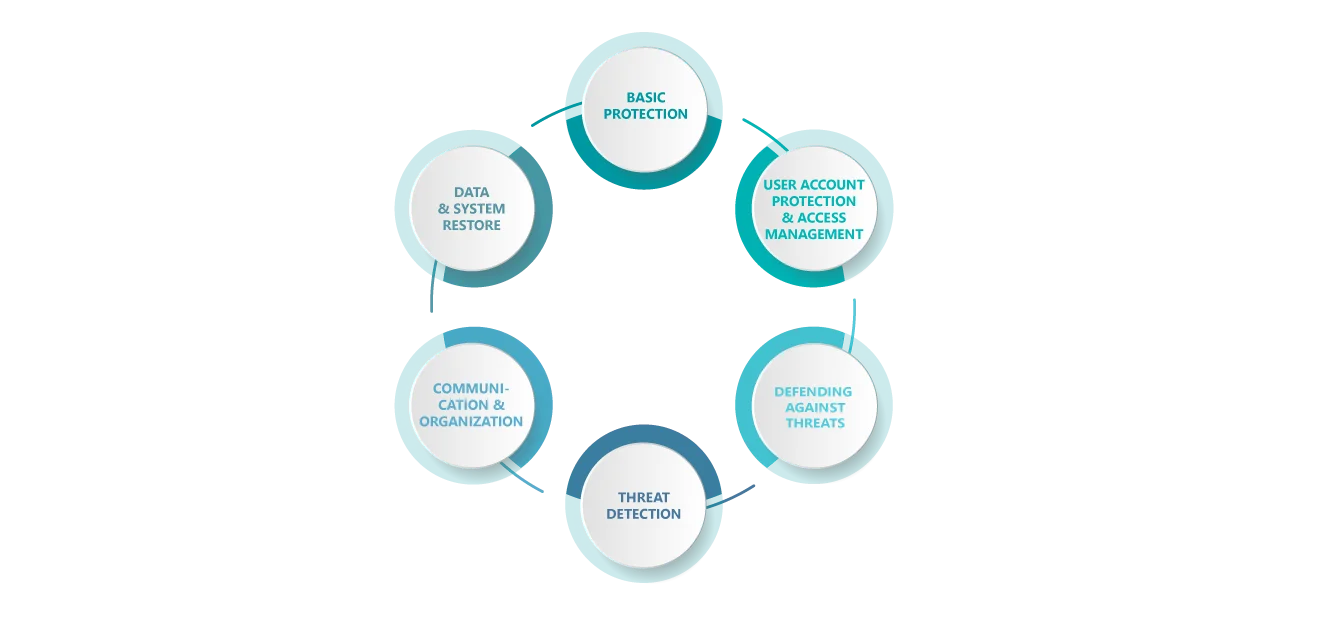
Your security concept – structured to include 6 areas of security
To make sure nothing essential is missed, we structure the security concept to include six key areas. That structure is deliberately flexible: Depending on the services and platforms in use (e.g. Microsoft 365, Azure, SaaS or on-prem systems), we can systematically expand the actions, so that the concept can grow in line with your IT landscape, without needing to be redrafted each time.
Trust is good, but verification is better.
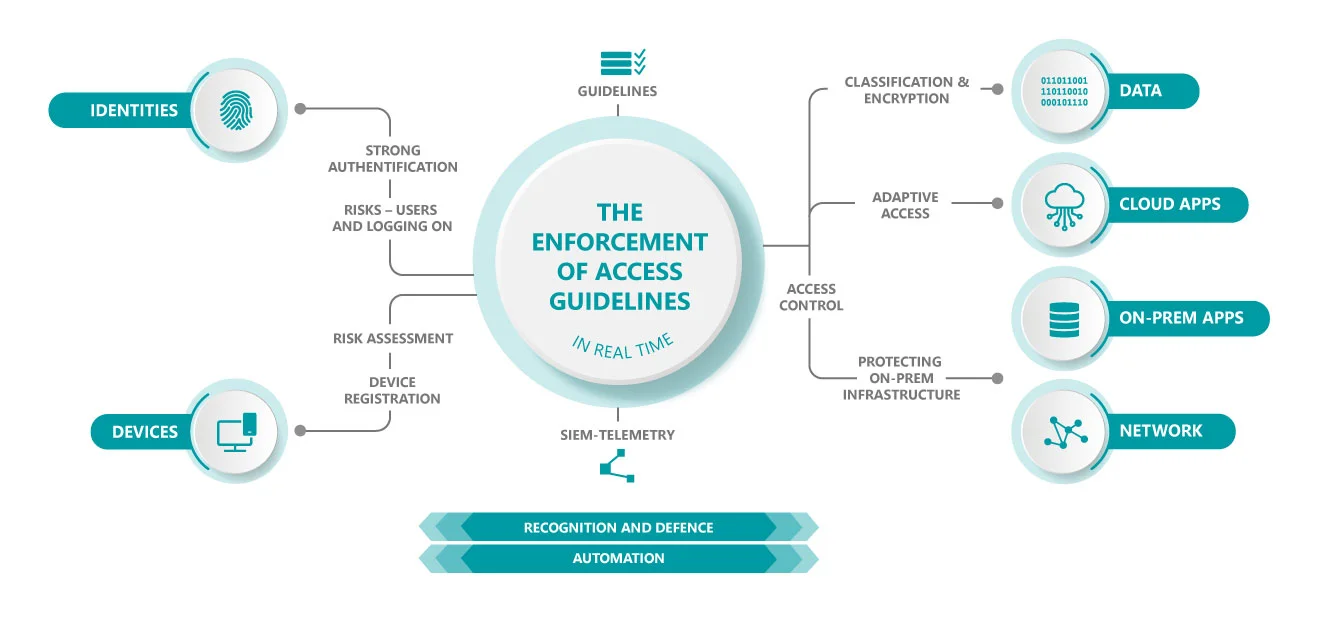
Zero trust: enforcing access guidelines in real time
In cloud-first and hybrid scenarios in particular, IT security often stands or falls on one point: how consistently access guidelines are enforced and what that decision is actually based upon. Zero trust means: trust is not implicit and access is only granted in accordance with clearly defined rules and continual verification.
In our security concept, we define the parameters for enforcing access guidelines in real time, including in relation to the following components:
robust authentication and evaluation of user-related risks and risks when logging on
device registration and risk assessment as the basis for trustworthy access
access control and adaptive access – depending on context and risk
data, cloud apps, on-prem apps and network
protecting sensitive information using clear rules and technical measures
visibility as the basis of detection and defence
defined responses and procedures as a means of acting more rapidly and consistently
These result in an architecture that combines security and user experience, without making operations too complicated.
How we work
Road map for the implementation of your security concept
We translate your vision into clear steps – from quick wins and stabilisation to achieving your vision of cloud-first/cloud-only. That way, you are still able to act, without overburdening your organisation:
What you will get at the end: a security concept, architecture & a road map
So that you can make well-founded decisions and plan implementation in a targeted way, you will receive the following documents and outcomes:
Making technologies usable
Security architecture for unitop: Roles, access and operations
When introducing and operating unitop – based on Microsoft Dynamics 365 Business Central – we take a holistic view of the security requirements right from the start. On the Microsoft platform, tried-and-tested security mechanisms can be used in conjunction with Microsoft 365 and Azure in a targeted way, to set up your unitop environment stably and securely. These include the following components:
Contact
Your contact for security concept & security architecture
Are you looking for a security concept that fits your environment and can be implemented on a practical level? We’ll be pleased to advise you.


